When customers pay online by credit card, cardholder data and other security-relevant payment information are processed. Businesses that accept credit card payments, integrate them technically, or influence the payment flow through their own systems are therefore subject to clearly defined security and control requirements. PCI DSS compliance refers to the demonstrable implementation of those requirements within the relevant payment environment.
The Payment Card Industry Data Security Standard (PCI DSS) is the primary security standard for companies and service providers that store, process, or transmit credit card data. Its purpose is not only to protect individual data elements, but to secure the broader environment in which cardholder data is processed or whose security can affect that data.
This is especially relevant in digital payments because card transactions now typically pass through multiple technical components, including websites, platforms, checkout systems, payment gateways, processors, and other connected payment infrastructure. The more complex this architecture becomes, the more important it is to define responsibilities clearly, identify which systems are in scope, and apply the appropriate security controls.
For online businesses, platforms, and payment providers, the key issue is therefore not only the standard itself, but the actual PCI DSS compliance of their specific setup. What matters is how security requirements are implemented technically and organizationally, which systems fall within PCI scope, and how the protection of sensitive payment data is demonstrated in ongoing operations.
PCI DSS as a Binding Security Standard for Cardholder Data
PCI DSS stands for Payment Card Industry Data Security Standard. It is not a general quality label for “secure payments,” but a binding control framework for companies and service providers that store, process, or transmit cardholder data or that can affect the security of the Cardholder Data Environment (CDE). The standard therefore defines the technical and operational baseline requirements that must be met to protect payment data in real payment environments.
PCI DSS was developed by the major card brands Visa, Mastercard, American Express, Discover, and JCB to create globally consistent security requirements for the handling of payment data. In substance, the standard is not limited to isolated security measures. It establishes a structured framework covering network security, access control, protection of stored data, secure transmission, logging, monitoring, and regular security testing. That is why PCI DSS is not merely a documentation or audit topic in practice, but fundamentally a matter of architecture, scope, and controlled operations.
For current classification, it is important that the Self-Assessment Questionnaires in use today relate to PCI DSS v4.0.1. The PCI Security Standards Council explicitly describes these SAQs as validation tools for SAQ-eligible merchants and service providers. This also makes clear that PCI DSS is never assessed in the abstract, but always in relation to the company’s actual technical setup, scope, and payment integration model.
In practice, PCI DSS therefore protects not only the checkout transaction itself, but the broader security-relevant environment in which payment data is handled or whose security can be affected. For online businesses, platforms, and payment providers, the standard becomes especially relevant when it is necessary to determine which systems are in scope, which controls apply, and how compliance is evidenced in ongoing operations.
Network Security → Data Encryption → Access Control → Security Monitoring → Secure Payment Processing
PCI DSS Compliance in Practice
Being PCI DSS compliant means that a company has not only identified the applicable requirements of the Payment Card Industry Data Security Standard (PCI DSS), but has also implemented them effectively within its payment environment and can demonstrate that implementation when required. The decisive factor is not merely whether credit card data is processed, but under which technical and organizational conditions that processing takes place. Compliance is therefore always a combination of security architecture, clearly defined processes, access control, evidence management, and ongoing verification.
Companies that accept credit card payments or integrate card processing into their business operations must ensure that their systems, payment workflows, and internal controls meet the requirements of the standard. This goes beyond securing individual servers or applications. What matters is the controlled assessment of the entire payment environment. The key questions are which systems come into contact with cardholder data, which components are security-relevant for the payment flow, and how access to sensitive data is restricted both technically and organizationally.
A core element of PCI DSS compliance is the ability to document the payment architecture in a clear and defensible way. Companies must be able to show where payment data is processed, which systems fall within scope, which protective measures have been implemented, and how security events are identified, logged, and assessed. In practice, this includes the secure storage and processing of cardholder data, the encryption of sensitive information during transmission, strict access controls for systems and personnel, regular security reviews, vulnerability assessments, and continuous monitoring of the overall payment infrastructure.
In addition, the exact validation and assessment obligations vary depending on company size, transaction volume, and technical integration model. Smaller merchants may, under certain conditions, qualify for a reduced self-assessment approach, while larger businesses, complex payment environments, or specialized payment service providers are usually subject to more extensive validation requirements. Depending on classification, this may include structured audits, formal compliance evidence, and assessments performed by qualified external parties.
PCI DSS compliance is therefore not a one-time status, but an ongoing process of security management and control. Companies must regularly review their payment environment, assess technical changes, and adapt their safeguards to evolving risks. Only this kind of continuous discipline ensures that credit card payments remain secure over time and that risks such as data leakage, fraud, or unauthorized access are effectively limited.
Which Businesses PCI DSS Applies To
The PCI DSS standard is generally relevant to all businesses that store, process, or transmit credit card data. In practical terms, this means that as soon as a company accepts card payments or technically integrates card processing into its payment operations, PCI DSS becomes relevant. What matters is not only whether cardholder data is stored on a permanent basis, but whether systems, processes, or service providers are involved in a way that affects the security of the payment environment.
PCI DSS therefore extends far beyond traditional online shops. In the modern digital economy, card payments are embedded in a wide range of business models, from e-commerce platforms and SaaS products with built-in payment functionality to marketplaces, subscription models, and international online services. Wherever credit card payments are processed or technically integrated, the requirements of the standard must be assessed and implemented appropriately based on the actual payment architecture.
PCI DSS is typically relevant for online shops and e-commerce businesses, digital platforms and marketplaces, software providers with integrated payment features, payment service providers and payment processors, operators of payment gateways or payment infrastructure, businesses with recurring credit card billing, and international online services with global card acceptance. Even companies that do not store card data themselves, but route transactions through external gateways, processors, or specialized payment providers, are not automatically outside the PCI context. The critical issue is how the technical integration is designed and which systems influence the payment flow or fall within scope.
This becomes especially important in complex payment environments such as platform businesses, marketplaces, creator ecosystems, or cross-border models with high transaction volumes. In these structures, it is not enough to rely solely on the compliance status of individual service providers. Companies must be able to assess which of their own systems, integrations, and internal processes are security-relevant and how responsibilities are distributed across the full payment architecture. This is particularly significant in high risk payment environments, where elevated fraud exposure, stricter risk controls, and stronger expectations around stability, monitoring, and security governance apply.
PCI DSS compliance in payment processing
PCI DSS compliance is a core element of professional payment infrastructure. Wherever credit card transactions are processed, the underlying system environment must be designed in a way that effectively protects cardholder data and ensures that only authorized systems, processes, and individuals can access security-relevant information. In practice, this is not about isolated security measures, but about the controlled protection of the entire payment architecture.
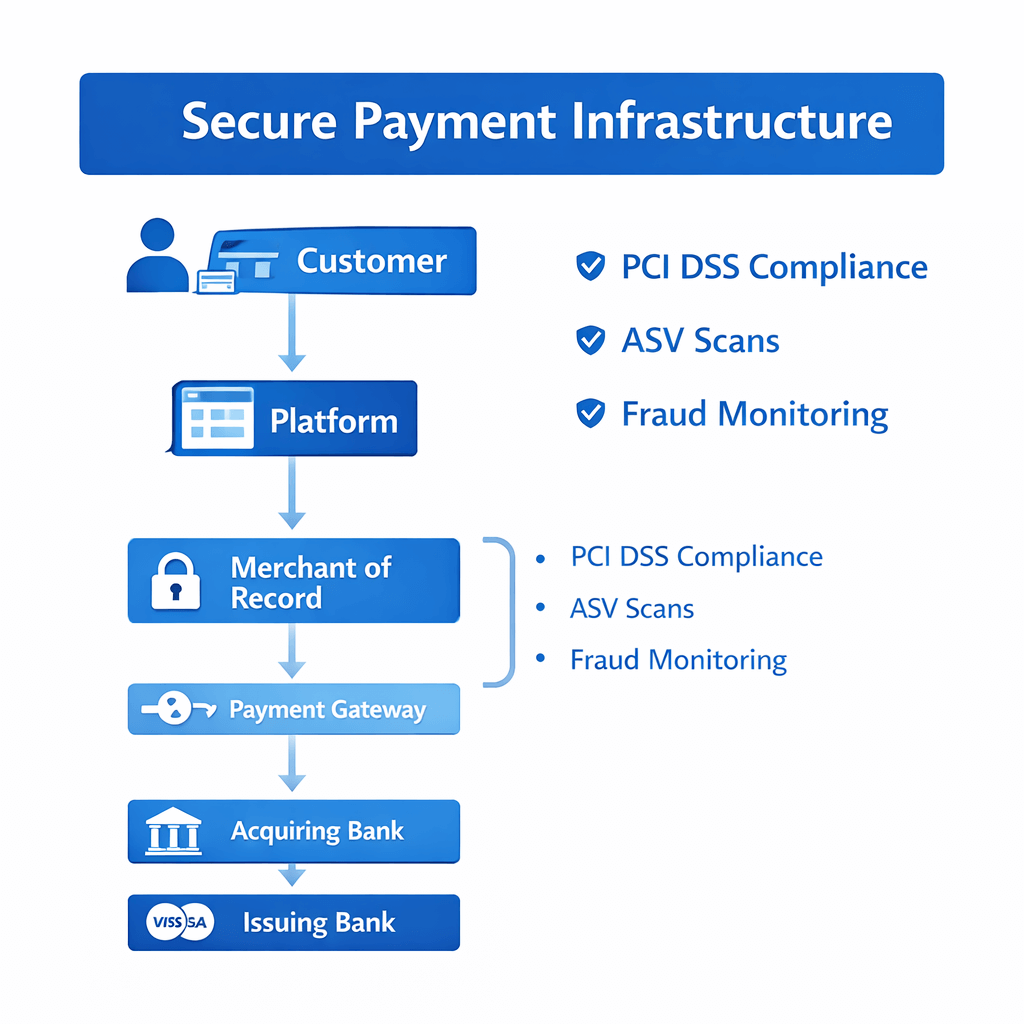
Within payment processing, a credit card transaction passes through several technical and regulatory stages. The flow typically begins at the checkout of a website or platform and continues through payment gateways, processors, acquirers, card networks, and issuing banks. Throughout this full chain of processing, security requirements must be applied consistently to ensure that payment data is neither transmitted insecurely nor handled within inadequately protected systems. This is where PCI DSS becomes operationally critical: the standard provides a binding framework for implementing and maintaining technical and organizational security controls across the full payment lifecycle. How this path runs operationally from the first controlled checkout to the issuer decision is outlined in from checkout to issuer.
This is especially important in high-risk payment processing environments. Business models with international customer bases, recurring billing, elevated chargeback exposure, or complex platform structures typically face higher requirements in terms of security, stability, and control depth. In these environments, it is not enough to make payments technically possible. What matters is that payment systems are resilient, properly governed, and protected against unauthorized access, misconfiguration, and security-relevant weaknesses.
This includes, in particular, secure payment gateways for handling card data, the encrypted transmission of sensitive payment information, hardened payment processing systems, structured transaction monitoring and logging, and the broader protection of the entire payment infrastructure against unauthorized access. Only the combined effect of these controls ensures that card payments are not merely processed, but processed within a security architecture that is robust and defensible.
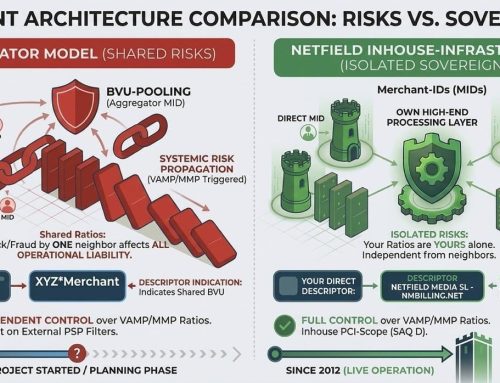
For that reason, consistent implementation of PCI DSS requirements is more than a formal compliance exercise. It is a technical and organizational prerequisite for processing credit card payments securely, reliably, and at scale in modern digital business models. The extent to which these requirements affect real-world architecture and compliance scope becomes particularly clear when comparing an aggregator model with a payment infrastructure that is controlled more directly.
The Role of Payment Gateways in a PCI-Compliant Payment Architecture
A payment gateway is a core component of modern payment infrastructure because it creates the technical connection between the checkout environment of a website or platform and the downstream payment systems involved in transaction processing. In practice, however, a gateway does far more than simply forward payment data. It is a security-relevant control point within the overall payment architecture and therefore has direct relevance for PCI DSS compliance.
From a technical perspective, a payment gateway acts as the interface between the customer-facing payment flow and the underlying payment participants, including processors, acquirers, card networks, and issuing banks. During a credit card transaction, payment information is received through the gateway, routed into a controlled processing flow, and forwarded for authorization to the relevant institutions. Because the gateway operates at a security-critical point in the transaction path, its implementation must ensure that sensitive data is not exposed, altered, or routed into insecure systems in an uncontrolled way.
For PCI DSS purposes, it is therefore not enough that a payment gateway is used. What matters is how it is integrated technically. An external gateway can reduce compliance scope, but it does not automatically remove the company’s own security responsibilities. The decisive question is whether the company’s own systems influence the checkout, client-side scripts, data flows, or other security-relevant components. This is precisely where the difference lies between a merely connected payment solution and a genuinely robust, PCI-compliant payment architecture.
Typical security capabilities of modern payment gateways include the encrypted transmission of card data, the secure processing of sensitive payment information, tokenization or masking of card details, the integration of fraud detection mechanisms, structured transaction monitoring and logging, and secured communication with processors, acquirers, and banks. These capabilities are security-relevant because they help ensure that payment data is not exposed or misused during transmission and further processing.
Especially in international online payments, platform models, subscription businesses, or complex multi-provider environments, a secure payment gateway is therefore not an optional convenience layer, but a foundational element of a controlled payment infrastructure. It supports reliable transaction processing between customer, platform, payment provider, and bank, reduces operational risk, and in many architectures serves as a key building block for handling cardholder data in a technically sound, traceable, and compliance-ready manner.
Merchant of Record and PCI DSS Compliance
A Merchant of Record (MOR) is strategically important in many digital business models because it does more than process payments technically. It acts as the formal merchant toward card schemes, acquirers, and other payment participants. For platforms, digital services, and international online businesses, this is particularly relevant where payment operations, regulatory responsibility, and scalable execution are not intended to be built entirely in-house.
Within this model, the Merchant of Record assumes key responsibilities across the payment infrastructure. These typically include accepting and processing credit card payments, managing the commercial side of the payment flow, handling chargebacks, and maintaining operational compliance with relevant security and regulatory requirements. In complex payment environments, this can significantly reduce the internal burden because a specialized provider brings standardized processes, controlled technical environments, and established compliance structures. For creators and platforms that want to use this model operationally, Netfield Media offers a payment infrastructure for creators and platforms.
In the context of PCI DSS compliance, however, one point requires careful clarification: a Merchant of Record can significantly reduce the compliance burden for the connected platform or digital business, but it does not automatically eliminate it in every integration model. What matters is how the technical setup is designed, which systems influence the payment flow, whether the company’s own checkout components remain security-relevant, and whether the platform itself still touches cardholder data or systems that fall within PCI scope. This precise allocation of responsibility is essential for a defensible compliance assessment.
An MOR model is often particularly suitable for businesses that process international online payments, operate subscription-based business models, manage creator, SaaS, or platform ecosystems, or run complex payment structures with high transaction volume. In these scenarios, companies benefit not only from operationally stable payment execution, but also from clearer processes around risk, control, and compliance evidence.
The real value therefore lies not simply in outsourcing isolated payment steps, but in shifting clearly defined responsibilities to a specialized provider in a structured way. Where architecture, role allocation, and data flows are designed correctly, a Merchant-of-Record model can help implement security requirements more efficiently while supporting a payment architecture that is scalable, resilient, and genuinely compliance-ready.
Customer → Platform → Merchant of Record (e.g. Netfield Media) → Payment Gateway → Acquiring Bank → Card Network → Issuing Bank
📌 NETFIELD MEDIA meets the requirements of PCI DSS SAQ D Merchant compliance, including the mandatory ASV scans. The verification record can be viewed here.
PCI DSS and modern payment infrastructure
In modern payment environments, security is not an isolated add-on, but a foundational element of the overall technical architecture. Companies that accept international online payments must operate payment systems that are not only performant and scalable, but also controlled, traceable, and aligned with recognized security standards. This is where PCI DSS becomes the key framework for the structured protection of cardholder data within a professional payment infrastructure.
The standard is so important because credit card transactions are no longer handled within a single system. A transaction typically moves through several technical stages, from the checkout environment to payment gateways, processing systems, acquirers, card networks, and issuing banks. In a modern infrastructure, this means that security cannot rely on isolated controls alone. What matters is the controlled interaction of the full architecture. The decisive factors include which systems fall within PCI scope, how networks are segmented, how access is governed, how payment data is transmitted, and how security-relevant events are detected, logged, and assessed.
Digital platforms, international online services, and subscription-based business models in particular depend on payment infrastructures that can handle high transaction volumes, cross-border payment flows, and complex technical integrations reliably. In these environments, functioning processes alone are not enough. What is required is an infrastructure that is secure, scalable, observable, and compliance-ready at the same time. This includes secure network architecture for payment data, encrypted transmission of sensitive card information, resilient payment gateways and processing systems, continuous transaction monitoring, effective fraud detection mechanisms, and systems that remain stable as international reach and operational complexity increase.
A modern PCI-compliant payment infrastructure therefore delivers much more than basic payment capability. It ensures that payment processes remain reliable, that security-critical risks are kept under control, and that companies can accept credit card payments globally without compromising the protection of sensitive payment data. For digital business models built for growth, this is not just a matter of security, but a core requirement for trust, operational stability, and long-term scalability. This applies in particular to specialized sectors such as Adult Payment, where payment processing, risk requirements, and compliance are especially closely interconnected.
SAQ A, SAQ A-EP, SAQ D Merchant, and ASV Scans
The PCI DSS requirements that a business must actually meet depend in practice not only on the fact that it accepts credit card payments, but above all on the specific technical architecture of the payment flow. The key question is whether the environment falls under SAQ A, SAQ A-EP, or SAQ D Merchant. This classification determines which controls must be validated, how far PCI scope extends, and which compliance path actually applies to the merchant. The PCI Security Standards Council explicitly provides the Self-Assessment Questionnaires as validation tools for environments that meet the relevant eligibility criteria.
SAQ A is intended for merchants whose account-data functions are fully outsourced to PCI-compliant third parties. In an e-commerce setup, this means that the payment page or payment form must be delivered directly from the PCI-compliant payment provider to the customer’s browser. As soon as the merchant influences the payment flow through its own web components, scripts, or page elements in a security-relevant way, this classification must be reviewed very carefully. This is exactly why SAQ A eligibility for e-commerce merchants was clarified in PCI DSS v4.0.1.
SAQ A-EP is intended for e-commerce merchants that do not electronically store, process, or transmit cardholder data themselves, but whose website affects the security of the transaction or the integrity of the payment page. In practice, this is highly relevant for many platforms, checkout integrations, and merchant-controlled web environments. Simply using an external PSP or payment gateway is therefore not enough by itself to place a business outside an expanded PCI scope.
SAQ D Merchant is the most comprehensive validation path for merchants and applies whenever a business does not cleanly fit into a narrower SAQ type or has additional PCI DSS requirements within scope. For complex architectures, heavily controlled checkout environments, or broader payment integrations, SAQ D is often the operative standard path in practice.
A particularly important topic in PCI DSS v4.x is ASV scanning. The PCI Security Standards Council defines Approved Scanning Vendors (ASVs) as qualified entities for external vulnerability scanning. The relevant control here is Requirement 11.3.2, which requires evidence of passing external vulnerability scans performed by an ASV. For SAQ A merchants, this topic became explicitly newly relevant with the future-dated requirements that took effect on 31 March 2025. In practical terms, that means ASV scans are now a much broader part of ongoing PCI validation, including in e-commerce environments that were previously treated as heavily outsourced.
In practice, businesses should therefore assess their payment architecture not only by asking whether an external payment provider is used, but how checkout pages, redirects, embedded payment forms, client-side scripts, and merchant-controlled web systems actually influence the payment flow. Only on that basis can a company determine reliably whether SAQ A, SAQ A-EP, or SAQ D Merchant applies, and which requirements, including ASV scans, must be validated on an ongoing basis.
PCI Scope, CDE, and Formal Validation
For the practical assessment of PCI DSS compliance, the key question is which systems are actually part of the Cardholder Data Environment (CDE). The CDE includes the systems, networks, and processes in which cardholder data is stored, processed, or transmitted. In addition, connected or security-relevant systems may also fall within PCI scope if they can affect the integrity or protection of that environment. This is why PCI DSS is, in practice, above all a matter of scope definition, segmentation, and technical boundary control.
Formal validation is equally important. Depending on the setup, compliance is typically evidenced through the relevant Self-Assessment Questionnaire (SAQ) together with the associated Attestation of Compliance (AOC). In broader or more complex environments, a formal assessment with a Report on Compliance (ROC) may be required instead. Such assessments are usually performed or supported by a Qualified Security Assessor (QSA) where the applicable model or acquiring bank requires it.
For merchants, the important point is that external providers may reduce PCI scope, but they do not automatically assume full responsibility. A PSP, payment gateway, or Merchant of Record only reduces burden to the extent that architecture, checkout logic, data flows, and control responsibility are truly outsourced. Every payment setup therefore requires a precise assessment of which systems remain under merchant control, which components are still security-relevant, and which validation path follows from that structure.
Conclusion
PCI DSS compliance is neither an abstract security concept nor a purely formal proof of “secure online payments.” In practice, PCI DSS is a binding control framework for the handling of cardholder data and is therefore directly linked to technical architecture, PCI scope, the Cardholder Data Environment (CDE), the allocation of responsibilities between merchants and service providers, and the ongoing validation of security controls. This is where the standard derives its real operational relevance: compliance effort is not determined simply by whether a business accepts credit cards, but by the actual design of the payment flow, the systems involved, and the security-relevant integrations that support it.
For businesses processing credit card payments in e-commerce, platform models, SaaS environments, or international online services, PCI DSS is therefore above all a matter of architecture, control depth, and demonstrable operational discipline. The critical questions are which systems are truly in scope, whether the environment falls under SAQ A, SAQ A-EP, or SAQ D Merchant, which requirements from PCI DSS v4.0.1 are actually applicable, and how those requirements are validated in ongoing operations. Depending on the model, this may include the relevant Self-Assessment Questionnaires, an Attestation of Compliance, formal assessments where required, recurring vulnerability management, and – where applicable – ASV scans as part of external security validation.
It is equally important to classify the role of external payment providers correctly. A PSP, payment gateway, or Merchant of Record can significantly reduce PCI scope and shift operational and regulatory burden in a meaningful way. It does not, however, automatically eliminate the merchant’s compliance responsibility. What remains decisive is which components stay under merchant control, how checkout pages, redirects, embedded payment forms, or client-side scripts are implemented, and whether merchant-controlled systems still influence the security of the payment process. This is precisely the point at which a formally outsourced payment setup differs from a genuinely robust, clearly delimited, and technically defensible PCI strategy.
For modern payment infrastructures, this means that PCI DSS compliance is not a one-time project, but an ongoing process of security management and validation. Companies must continuously monitor their payment architecture, assess technical changes in a controlled way, assign responsibilities clearly, and keep their compliance evidence up to date. Businesses that approach PCI DSS in this way do not only protect sensitive credit card data; they also build the foundation for stable, scalable, and trustworthy payment operations in demanding digital business models.
FAQ
Is an external payment provider enough to eliminate a merchant’s PCI scope?
No. An external PSP, payment gateway, or even a Merchant of Record can significantly reduce PCI scope, but it does not eliminate it automatically. The decisive factor is whether merchant-controlled systems still influence the payment flow, checkout, embedded payment forms, redirects, or client-side scripts in a security-relevant way. That technical integration determines which systems remain in scope and which obligations still remain with the merchant.
What determines whether SAQ A, SAQ A-EP, or SAQ D Merchant applies?
The classification depends on the actual payment architecture. SAQ A is limited to heavily outsourced models in which the payment page or payment form is delivered directly from the PCI-compliant third party to the customer’s browser. SAQ A-EP applies where the merchant does not itself store, process, or transmit cardholder data, but its website affects the security of the transaction or the integrity of the payment page. SAQ D Merchant is the comprehensive validation path for more complex environments or setups that do not qualify for a narrower SAQ.
What role do redirects, embedded payment forms, and client-side scripts play?
They are central to scope assessment. Redirects and embedded payment forms can help outsource the direct handling of cardholder data, but they do not change the fact that merchant-controlled websites may still remain security-relevant. Client-side scripts in particular are a critical issue under PCI DSS v4.x because the integrity of the payment environment must be protected and monitored.
What is the difference between PCI scope and the Cardholder Data Environment?
The Cardholder Data Environment (CDE) is the part of the environment where cardholder data is stored, processed, or transmitted. PCI scope can extend beyond that, because connected or security-relevant systems may also be included if they can affect the security of the CDE. In practice, that distinction matters because not only systems with direct card data are relevant, but also adjacent components that affect protection, integrity, or access control.
When are ASV scans relevant?
ASV scans are relevant where the applicable PCI DSS setup requires external vulnerability scans by an Approved Scanning Vendor. The key control here is Requirement 11.3.2. Since the future-dated requirements took effect on 31 March 2025, this has become materially more relevant for certain e-commerce setups, especially where updated SAQ requirements apply.
Which PCI DSS evidence is typically required in practice?
That depends on the environment. Commonly relevant evidence includes the appropriate Self-Assessment Questionnaire (SAQ), the Attestation of Compliance (AOC), and in broader assessments a Report on Compliance (ROC). In more formal or complex environments, a Qualified Security Assessor (QSA) may also be involved. The exact evidence required depends on the acquirer, card program requirements, and the merchant’s actual compliance model.
Can a Merchant of Record fully take over PCI responsibility?
Not automatically. A Merchant of Record can take over major operational, regulatory, and technical responsibilities and thereby significantly reduce PCI burden for the connected platform or merchant. Whether responsibility is fully shifted depends on the actual allocation of roles, checkout architecture, data flows, and which systems remain under merchant control.
Why is PCI DSS not a one-time project, but an ongoing validation process?
Because PCI DSS requires not just the one-time documentation of controls, but their ongoing effectiveness. Depending on the setup, this includes recurring reviews, vulnerability management, evidence collection, monitoring, logging, change control, and repeated validation. Compliance must therefore be maintained continuously and adapted to technical changes, new risks, and modified integrations.