From checkout to issuer is not just a process description in e-commerce, and it is not a theoretical architecture diagram. It is the technical and operational path on which it is decided whether a card payment is merely accepted or processed inside a controlled and resilient structure.
What is publicly visible is usually only the checkout. This is where the user enters card data, confirms a payment, and later sees only whether it succeeded or failed. For the operator, however, the real relevance does not sit in that visible moment, but in the path behind it. That is where the part of payment begins that determines stability, traceability, security, and commercial resilience.
Between card entry and the issuer’s decision, there are not just a few technical steps. There is data capture, scope, technical handover, processing, routing, MID structure, acquiring, scheme logic, and 3-D Secure. This is the path where it becomes clear whether a setup merely passes payments through or whether real payment infrastructure is working behind it.
This is not an academic distinction. In practice, this part decides whether a system stops at the first decline, whether transactions run rigidly through only one path, whether technical friction costs unnecessary approval, and whether critical parts of processing sit outside the operator’s own structure. Anyone speaking about secure card payments therefore cannot stop at the form. What matters is where card data is collected, how the handover into processing is built, which instances are involved in routing and acquiring, and whether the path to the issuer is actually under control.
The cardholder only sees the result later. For the operator, the real truth lies in the path leading to it. That is where it is decided whether a payment path is traceable, controllable, and durable over time — or only appears to be.
Secure Card Payments Start at Checkout
Checkout is the point at which purchase intent turns into a security-relevant processing event. As long as a user is moving across offer pages, landing pages, or content pages, the surface is still in the foreground. The moment card data is entered, that changes. From that point on, the issue is no longer just usability or conversion, but the environment in which sensitive data is captured and how it is handed over into the downstream payment path.
This is exactly where a simple redirect or gateway setup is separated from real infrastructure. A checkout is not just a form placed in front of an acquirer. It is the entry point into a technically separated area where scope, data flow, responsibility, and later control are defined. If this entry point is built poorly, the path behind it remains dependent, rigid, and externally controlled at too many points.
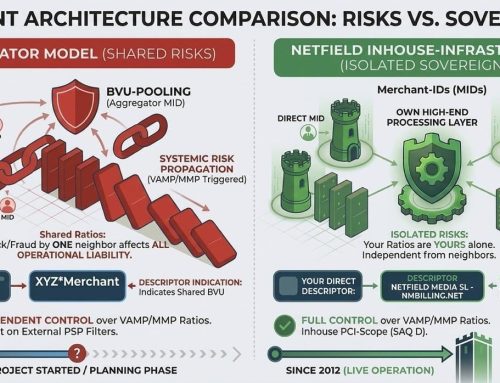
For Netfield Media, this is where a key difference begins. We do not work with a mere handoff into a single external flow. We work with a structure in which our own checkout, our own processing layer, multi-acquirer routing, and multi-MID logic run together. We set up MIDs ourselves, manage processing ourselves, and therefore control not only the surface, but the operational path behind it as well. That is what makes fallbacks, smart routing, and alternative acceptance paths genuinely usable — not as an after-the-fact workaround, but as part of one connected system.
This is why PCI compliance matters here not as a formal appendix, but as a technical requirement for a cleanly separated payment environment. The PCI Security Standards Council describes PCI DSS as a baseline of technical and operational requirements for environments where payment account data is stored, processed, or transmitted. That is the real point here: not simply that card data is entered securely in some way, but that data capture, handover, and processing are built in a way that control is not lost at the first interface.
What later becomes visible as an authorization or charge starts exactly here. That is why checkout does not belong in the design corner, but in the core of payment architecture. This is where it is decided whether a card payment is merely accepted — or whether it runs from the start inside a controlled, steerable, and resilient infrastructure.
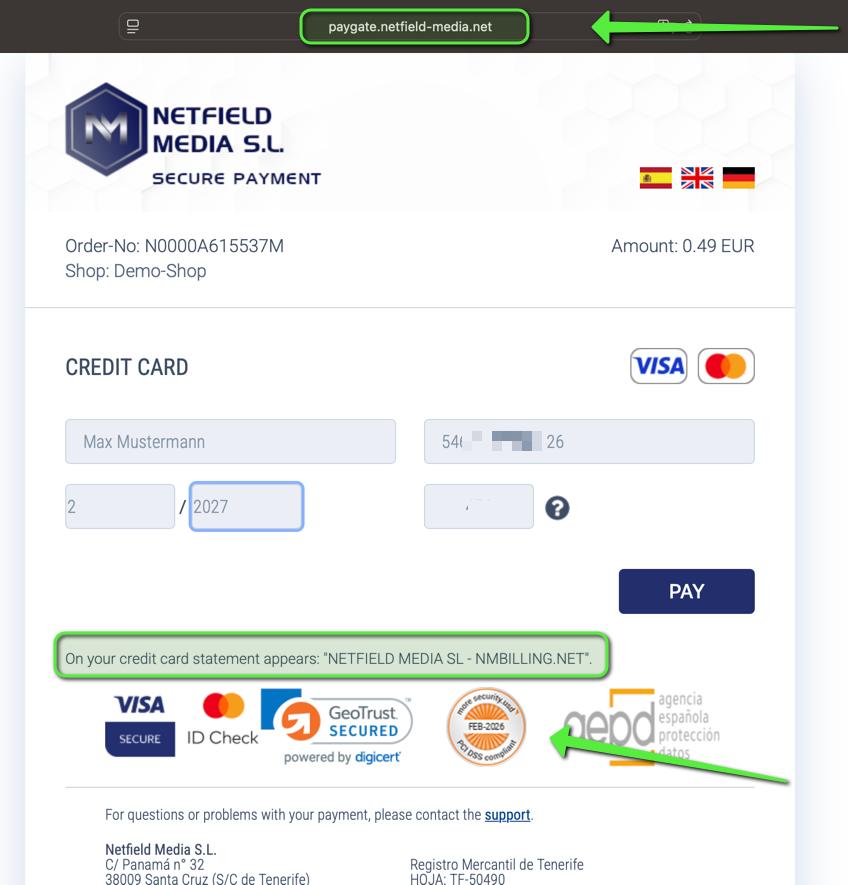
Screenshot of the isolated Netfield checkout form – sensitive data blurred
The Path From Checkout to Issuer
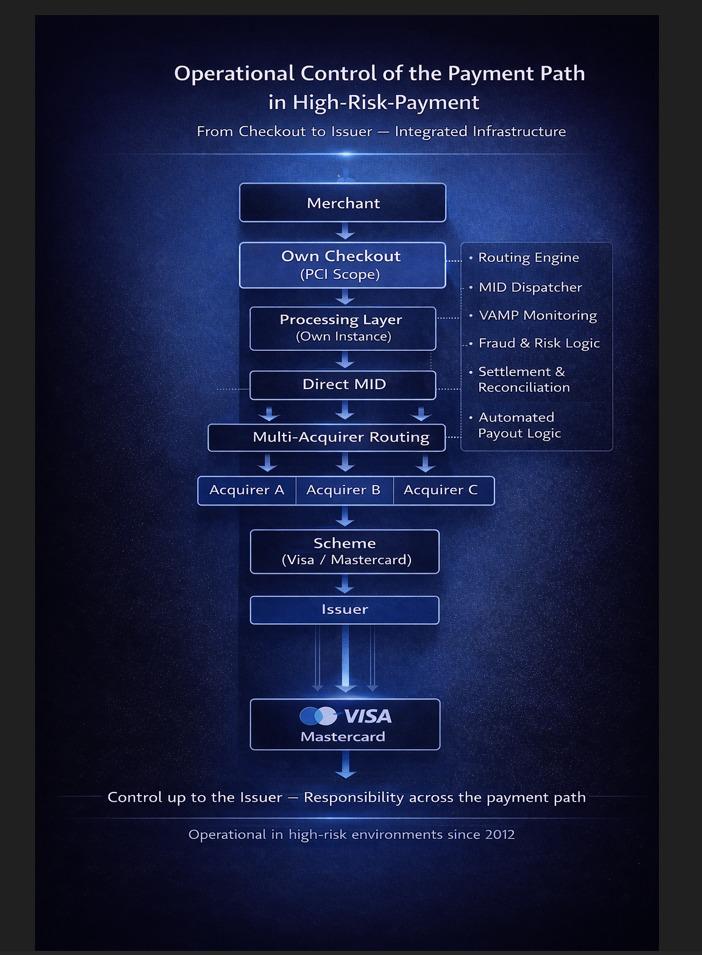
The path from checkout to issuer remains invisible to the cardholder, but it is decisive for the operational assessment of a payment. Card data is not simply “sent to the bank.” Between capture and the issuer’s decision lies a technical processing path on which data is handed over, transactions are assigned, responsibilities are defined, and bank-side routes are prepared. This is exactly where it becomes clear whether a structure is based on simple forwarding or built as a controlled payment path.
The route does not run directly from the form to the issuer. After checkout come processing, MID, acquirer, and scheme, before the issuer makes the actual decision. Each of these layers has its own function. Together, they form the operational logic of the transaction. Anyone who shortens this sequence or treats it as a technical given underestimates the very part of card processing where the resilience of a setup becomes visible.
For Netfield, this path is not an external black-box process. Through our own processing layer, we set up MIDs ourselves, manage processing ourselves, and keep routing and operational logic not just at the surface, but inside the same structure. That is exactly what allows fallbacks, smart routing, and alternative acceptance paths to work inside one connected flow, instead of being added from the outside only after a decline. Standard processing often ends with the first “no” from the bank. Our structure is built specifically not to stop there. It is built to continue working within its own path when one route does not hold.
This is also where it becomes clear why payment infrastructure means more than simply connecting a payment form. Infrastructure shows itself where handovers are defined, technical dependencies are limited, and processing steps are organised in a traceable sequence. The difference does not sit in the surface, but in the path behind it. That is where it is decided whether payments are passed through rigidly — or whether a system has the depth required to process transactions cleanly, under control, and in an economically sound way.
Diagram: “From checkout to issuer” – clearly illustrating the organisation’s own processing instance, Direct MID and multi-acquirer structure
Control Before Authorization
Before the issuer evaluates a payment at all, a substantial part of the path has already been completed. It is in this upstream area that it is decided whether a transaction is built, enriched, and handed over in a way that is technically consistent, traceable, and resilient. The point is not to anticipate the issuer’s decision. The point is to control the conditions under which that decision is made in the first place.
That requires far more than simply forwarding payment data. What matters is the structure of the data flow, the handovers between the involved layers, the clean assignment of transactions, the MID logic, and the question of whether responsibilities are clearly defined along the path. Anyone looking only at the moment of authorization misses the very part of card processing in which the real quality of a setup is created.
For Netfield, control therefore does not begin at the acquirer, and certainly not only at the issuer. Through our own processing layer, we keep MID setup, processing, routing, and operational logic inside our own structure. That is exactly what makes it possible not only to hand over transactions cleanly, but also to steer them within the same path. Fallbacks, smart routing, and alternative acceptance paths do not exist as external emergency fixes, but as part of an architecture built around control before authorization. Standard processing often ends with the first “no” from the bank. A resilient structure has to start earlier.
This difference becomes especially visible in high risk payment. Where acquirers review more strictly, tolerances are lower, and disruptions have immediate economic impact, a process that merely works on paper is not enough. This is where it quickly becomes clear whether a payment path is operationally under control or whether it only appears stable for as long as no deviation, no follow-up question, and no technical friction occurs. Control before authorization is therefore not a theoretical nuance, but a practical difference in the resilience of the entire path.
3-D Secure
Between upstream processing and the issuer’s final decision, many card payments include an additional step: 3-D Secure. For the cardholder, it usually appears only as a short confirmation in a banking app or another approval method. Operationally, however, this step is far more than a security prompt in the frontend. It is part of the same payment path and marks the point at which the cardholder’s authentication is checked separately before the actual authorization.
That is exactly why 3-D Secure must not be described as a mere scheme add-on. A transaction does not simply run from checkout to acquirer and from there to issuer. In between sits a technical and operational section that directly affects friction, drop-offs, confirmation quality, and approval behaviour. Anyone who downplays this part underestimates one of the points at which transactions are unnecessarily lost in practice.
For Netfield Media, 3-D Secure is therefore not an external extra step outside the actual payment logic. Through our own processing layer, 3DS also runs inside the same controlled structure as checkout, MID logic, routing, and acquiring. That is exactly what makes it possible not only to authenticate a transaction, but also to continue it cleanly within the same orchestration if one path does not hold. This is not about blind repetition. It is about controlled alternative acceptance paths inside a structure built precisely for that purpose. Standard processing often ends with the first “no.” Our path is designed to have more control before that point and within it.
Operational reality shows the quality of a setup very clearly at this point. If 3-D Secure is integrated poorly, if redirects create additional friction, or if the overall path is built too rigidly, this is exactly where problems arise that later show up as lost payments. That is why 3DS must not be viewed in isolation, but as part of the full processing chain. The operational effect is measurable: a cleanly orchestrated path reduces 3DS issues, technical declines, redirect drop-offs, and lost subscription payments.
3-D Secure is therefore neither a side issue nor a formality. It is its own point of load inside the payment path. Anyone describing the route from checkout to issuer properly has to do more than mention this step. It has to be placed in its operational context. This is exactly where it becomes clear whether authentication is part of a controlled payment architecture — or becomes a source of failure itself.
The Issuer Decision
Even along the path from checkout to issuer, the final decision remains with the issuer, not with the merchant. Only at this point does a technical handover become an actual approval or decline. For the cardholder, this usually appears as nothing more than an outcome. For the payment path, it is the end of a process that has already been built, checked, and prepared across multiple layers.
The issuer does not decide in a vacuum. The decision is made on the basis of what is presented along the path in a technically and procedurally ordered form. That is exactly why it is too narrow to define payment security only at the moment of the issuer’s decision. Authorization is not the beginning of transaction quality. It is its final checkpoint. What becomes visible there is the result of the path before it: data capture, handover, processing, MID logic, routing, acquiring, 3-D Secure, and technical consistency.
For Netfield, this is exactly where the operational difference lies. We do not make the issuer’s decision ourselves. But we control the path on which that decision is based. Through our own processing layer, we keep MID setup, processing, routing, and alternative acceptance paths inside our own structure. This avoids a rigid one-time pass-through and creates a properly built transaction logic in which technical friction, unnecessary drop-offs, and avoidable losses can be reduced before the issuer’s decision is reached. That is where the part of payment quality is created that the cardholder does not see later, but that acquirers, schemes, and operators certainly feel.
That is why secure card payment should not be reduced to approval and decline. The issuer’s decision is the final instance, but not the only relevant one. Anyone looking only at that point sees the end of the path, not its quality. The decision remains with the issuer. The conditions under which it is made are created beforehand — and that is exactly where it is decided whether a setup merely works formally or truly holds operationally.
What the Cardholder Sees
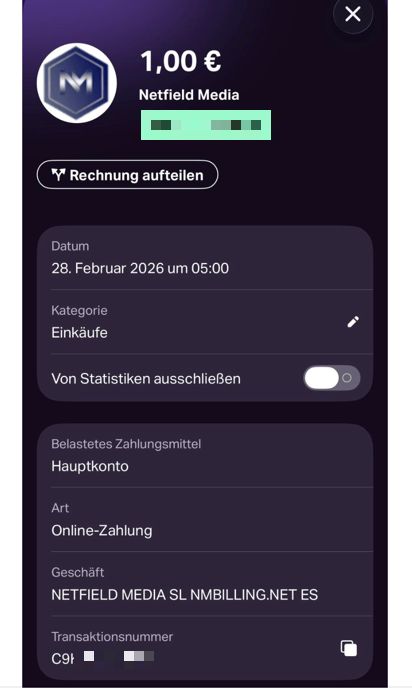
At the end of the path, the cardholder usually sees only a heavily reduced picture of the transaction. In the banking app, online banking, or on the card statement, what appears is a charge, a descriptor, and sometimes the booking date. The actual depth of the processing is no longer visible at that point. What is visible is the outcome, not the path that produced it.
That is exactly where a key difference between user perception and payment architecture becomes visible. What looks like a single card charge on the customer side is in reality the result of a process that started much earlier and passed through multiple layers. The cardholder does not see the checkout, the processing, the routing, or the technical decisions made upstream. What they see is only the moment in which that path becomes a booking entry.
This is precisely why that final visible layer is operationally more important than it may seem at first glance. The descriptor is not just a display line on a statement. It is the point at which recognisability, trust, and customer-side classification come together. If a payment appears unclear, unfamiliar, or implausible there, friction starts exactly at the point where the cardholder has no visibility into the upstream path anymore. This is especially relevant in adult payment, where discretion, recognisability, and clean assignment are not secondary details, but factors with direct impact on customer inquiries, refund risk, and chargeback behaviour.
From an architectural point of view, the charge is therefore not the transaction itself, but its visible conclusion. For the technical assessment of a secure card payment, the booking entry alone is not enough. For the cardholder, however, this point is decisive, because trust is not built on the invisible path behind the transaction, but on what actually appears on the statement, in the banking app, or in the card account. That is exactly why processing, descriptor logic, and outward visibility have to be built just as cleanly as the path before them.
Screenshot of a real credit card transaction in the banking app – sensitive data blurred
Conclusion From Checkout to Issuer
The path from checkout to issuer is not a decorative process chart and not a technical sublayer that can be ignored mentally. It is the part of card processing in which it is decided whether a setup can only accept payments formally or whether it truly holds up operationally.
Anyone measuring payment quality only at the visible checkout or at the final approval is looking at too little. The real quality is created before that: when card data enters a controlled environment, during technical handover, in processing, MID logic, routing, acquiring, 3-D Secure, and in the question of whether the full path is actually under control. This is exactly where a simple redirect or gateway flow is separated from a structure that can do more than mere payment acceptance.
For Netfield, this is the operational core. Through an own checkout, own processing layer, multi-acquirer routing, and multi-MID structure, the path does not simply stop at the bank’s first “no.” It is built to continue working within the same controlled logic, use alternative acceptance paths, and reduce technical losses before they become economically visible. The result is not only more control, but also fewer redirect drop-offs, fewer technical declines, fewer 3DS issues, fewer lost subscription payments, and ultimately more revenue from the same traffic.
That is exactly why secure card payment should not be reduced to approval and decline. The issuer’s decision remains the final instance. But the operational quality of the payment is created before that. Anyone who controls this path is not building a surface with a payment function, but a resilient payment architecture.
How this logic is translated into a full operator structure for creator and platform models is shown here:
Payment Infrastructure for Creators and Platforms
FAQ From Checkout to Issuer
Why is a visible checkout not enough to assess the quality of a card payment path?
A visible checkout shows only the entry point. It does not show how the path behind it is built. Whether card processing is truly resilient is decided further downstream: in processing, MID setup, routing, 3-D Secure, descriptor logic, and acquiring. That is where it becomes clear whether a system merely accepts payments or whether it is technically and operationally built to remain stable under friction, declines, and follow-up issues. The real difference therefore does not sit in the form, but in the infrastructure behind it.
Why is an own processing layer so critical for high-risk projects?
Because real control only begins where the operational logic is not fully handed over to an external standard flow. With an own processing layer, MID structures, routing decisions, fallbacks, and alternative acceptance paths can be controlled inside the same architecture. That is exactly why the path does not automatically end at the first technical or bank-side obstacle. The flyer states this logic directly: instead of rigid one-way processing, alternative paths are used to reduce redirect drop-offs, technical declines, 3DS issues, and lost subscription payments.
Why is customer-side trust in adult payment a technical factor and not just a communication issue?
Because trust in card payments is not created only in support communication. It starts at the point where the cardholder later recognises the payment on the statement or in the banking app. Especially in adult payment, the clean combination of descriptor, recognisability, discretion, and technical consistency often determines whether a payment is accepted, questioned, or later disputed. In adult and other high-risk environments, trust is therefore not a soft topic, but part of operational payment stability.
What is the practical purpose of the demo shop?
The demo shop is there to make the visible beginning of the path understandable in practice. It shows how the user enters the payment process, how the checkout behaves, and where card data capture begins. It does not replace the operational infrastructure behind it. That is why the demo shop is useful for understanding the start of the path, while the actual depth only becomes visible in processing, routing, MID logic, 3-D Secure, and the full downstream handling.